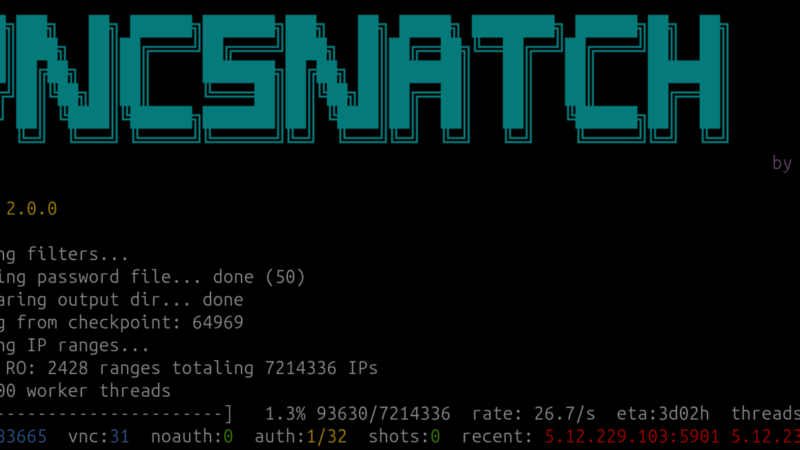
Every now and then, a side project turns into something slightly more uncomfortable than expected. vncsnatch started out like that for me: a technical curiosity, a small tool to explore how widespread exposed VNC servers really are, and how easy it is to get a visual impression of what’s sitting on the other end.
What I found was… not great.
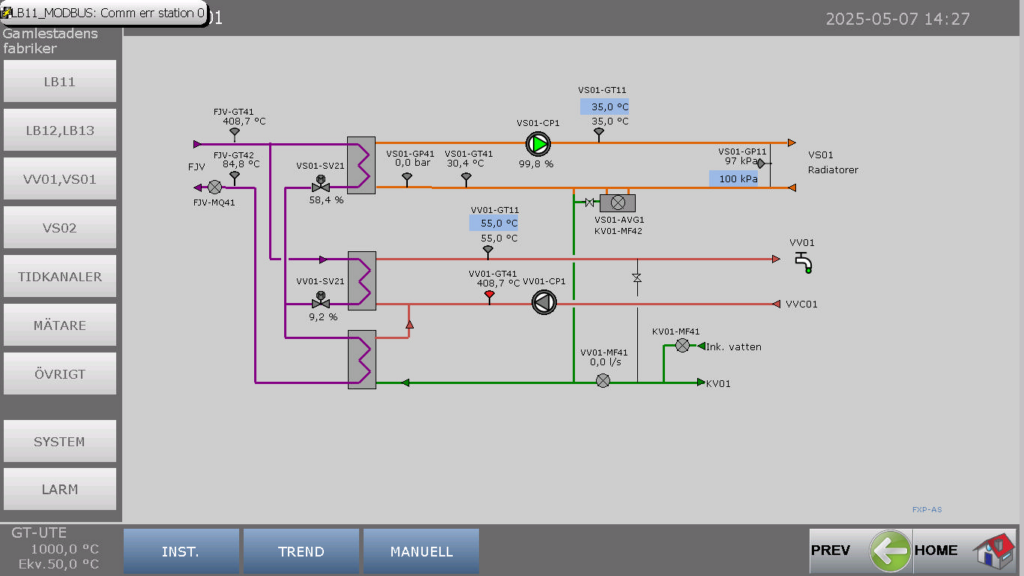
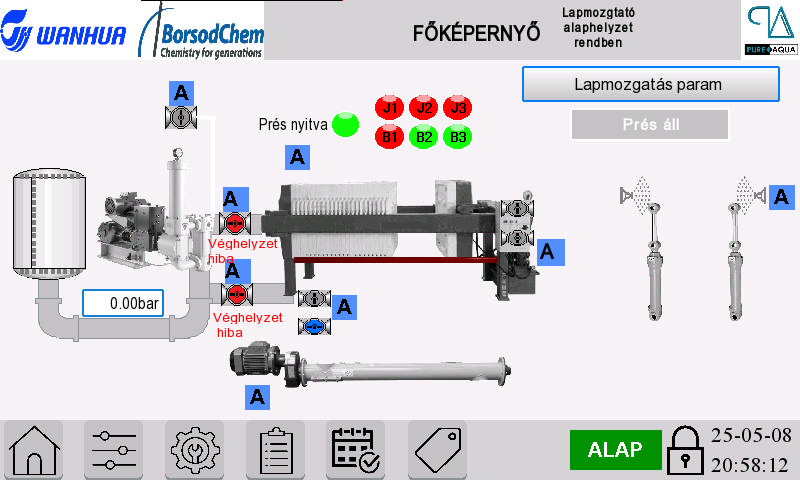
For anyone unfamiliar with the space: VNC is still widely used in industrial control systems, building management, energy monitoring, water treatment dashboards, heating systems, and other pieces of infrastructure that most of us implicitly trust to “just work.” In many cases, these systems are directly reachable from the internet. Sometimes they’re protected by a password. Often it’s weak. Occasionally, there’s no authentication at all.
vncsnatch exists to demonstrate just how trivial it is to discover and visually inspect these systems at scale. It does not exploit anything. It does not bypass authentication (unless you force it to). It simply connects, negotiates the protocol, and grabs a screenshot — exactly what any standard VNC client would do.
That’s precisely the problem.
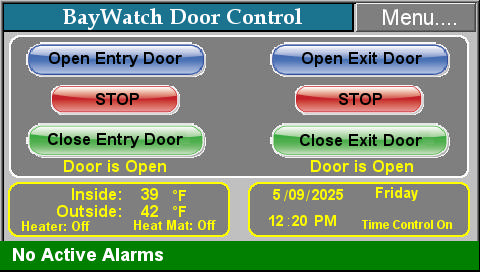
When I initially started working on vncsnatch, I did a quick scan of a limited set of IP addresses in Denmark. I wasn’t hunting for obscure edge cases – just the low-hanging fruit. The results included several systems that were, frankly, alarming: interfaces that strongly suggested links to critical infrastructure such as heating control, energy systems, and industrial monitoring.
I did what you’re supposed to do. I reported the most critical findings to the relevant organizations. Clear descriptions, screenshots, and an explanation that this was visible to anyone on the internet.
I received no response at all.
No acknowledgment. No “thanks, we’ll look into it.” Just silence.
That silence is, in many ways, more worrying than the exposed systems themselves. It suggests a mindset where security warnings are either not understood, not prioritized, or quietly ignored because “nothing bad has happened yet.” That is not a strategy. That’s wishful thinking.
This is where vncsnatch becomes more than just a tool. It’s a mirror. It shows how much critical infrastructure security still relies on obscurity, legacy setups, and the assumption that “nobody would look there.” The internet does not work like that anymore. It hasn’t for a long time.
With vncsnatch 2.0.0, the project has taken a solid technical step forward. Earlier versions relied on the external vncsnapshot tool to capture screenshots. That dependency is now gone. The application contains its own VNC screenshot implementation, making it more portable, more predictable, and easier to audit seen from a security and maintenance perspective. Less glue, fewer moving parts, fewer excuses. It has also gone full multithreaded for speed + much more.
The release doesn’t change the core idea of the project, but it does sharpen it. Vncsnatch is not about mass exploitation or sensationalism. It’s about demonstrating exposure in a way that’s impossible to ignore. A port scan can be dismissed. A screenshot of your control system on someone else’s laptop is harder to wave away.
There’s a recurring argument I hear from organizations in this space: “These systems are old,” or “They were never designed to be internet-facing.” Both may be true – and both are irrelevant. If a system controls water, heat, electricity, or other essential services, then its security posture matters regardless of its age or original design assumptions.
Connecting legacy systems to the public internet without proper isolation, strong authentication, and monitoring is not technical debt anymore. It’s operational risk.
Vncsnatch will continue to exist, not because I enjoy pointing out failures, but because the problem itself stubbornly continues to exist. Tools like this shouldn’t be necessary — yet here we are.
If you’re responsible for systems like these and this post makes you slightly uncomfortable, that’s a good starting point. Discomfort is often the first step toward fixing things.
You can find the project here:
https://github.com/kimusan/vncsnatch
And yes – it still finds far more than it should.
PS: if you do not want to scan the internet with vncsnatch to see what I am talking about, then go to vncresolver (the site that originally gave me the ideas for this project)