Stop trusting cloud providers with your personal data. Here is how to use rclone to build a transparent, client-side encryption layer over Dropbox or pCloud
2026
29
Apr
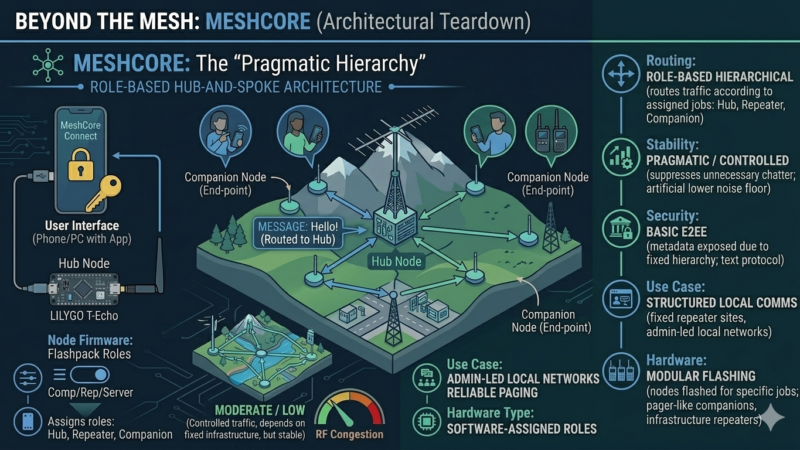
Beyond the Mesh: The MeshCore Paradime
Readers demanded to know where MeshCore fits into the off-grid landscape. It fixes RF congestion by forcing your radios into strict hierarchies. Here is why role-based routing is a brilliant band-aid but a severe regression for peer-to-peer sovereignty
24
Apr
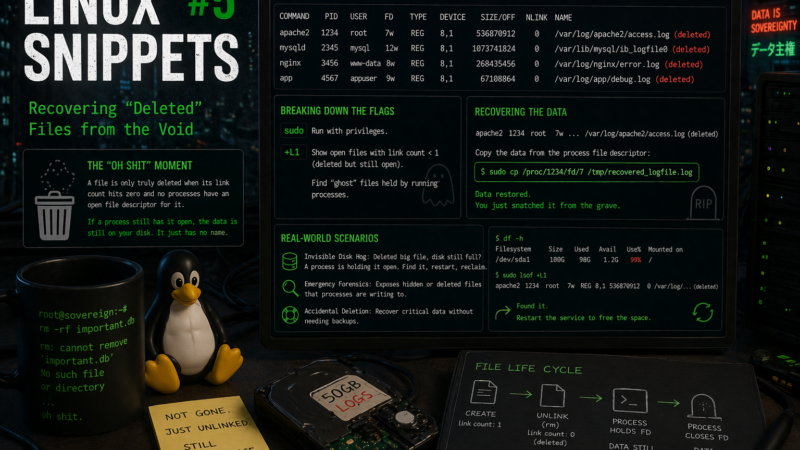
Linux Snippets #5: Recovering “Deleted” Files from the Void
Accidentally ran rm on a massive log file or a database while a process was still writing to it? Before you panic, learn how to use lsof to find the ‘ghost’ file in the /proc filesystem and snatch your data back.
23
Apr
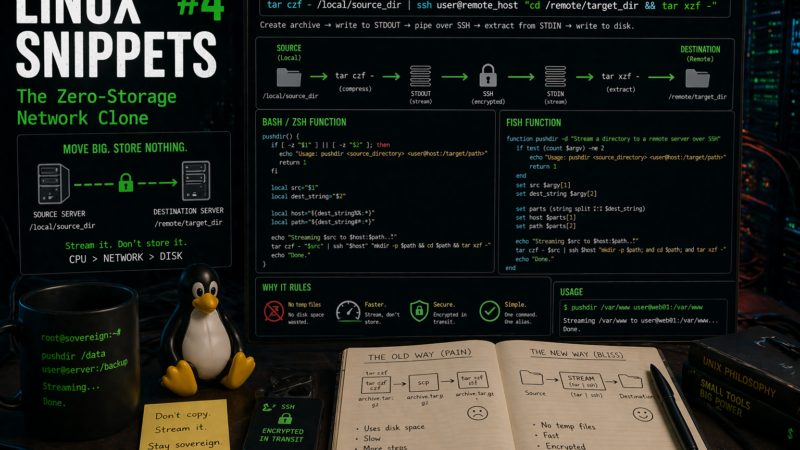
Linux Snippets #4: The Zero-Storage Network Clone
Stop filling up your disk with temporary zip files. Here is how to stream a directory directly from one server to another using tar and SSH in a single pipeline.
20
Apr
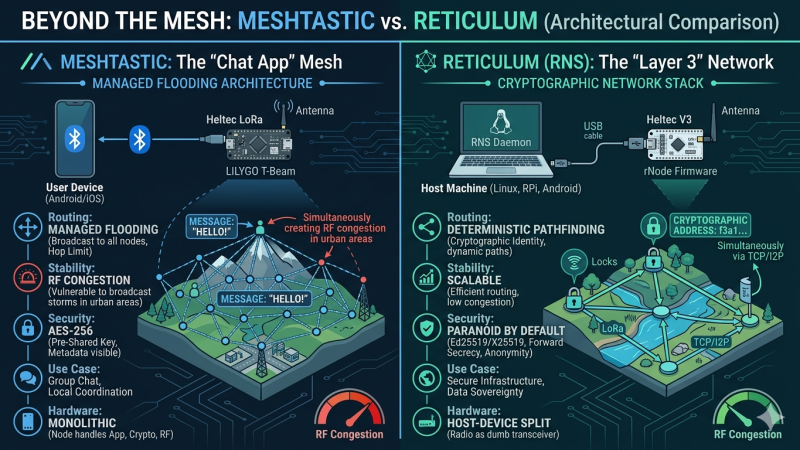
Meshtastic vs Reticulum: Why Reticulum Wins for Scalable Sovereign LoRa Networks
Meshtastic is currently dominating the off-grid communication hype cycle. But when we look under the hood at its managed flooding architecture and symmetric cryptography, does it actually hold up as a foundation for sovereign infrastructure? Here is a deep dive into why I am shifting my focus to the Reticulum Network Stack.
10
Apr

Linux Snippets #3: The Instant SSH SOCKS Proxy
Skip the heavy VPN clients. Here is how to turn any remote Linux server into an encrypted SOCKS5 proxy with a single SSH command to bypass hostile local networks
05
Apr
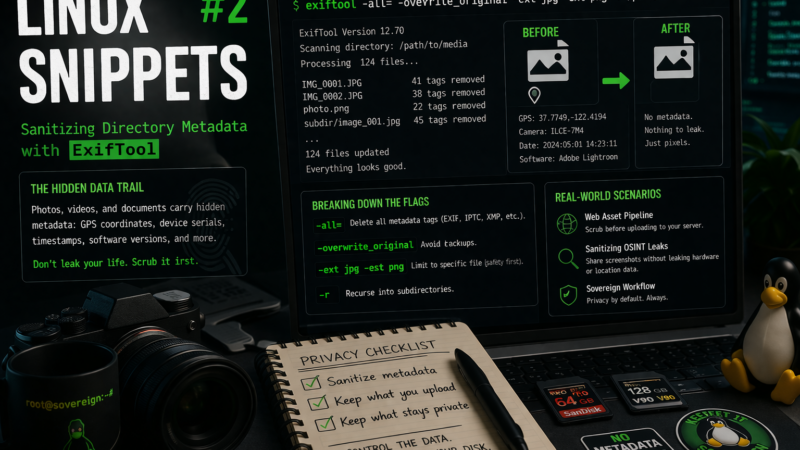
Linux Snippets #2: Sanitizing Directory Metadata with ExifTool
Blindly uploading images to the web is a massive privacy leak. Here is how to use exiftool to recursively strip hidden GPS and hardware metadata from your staging directories before they ever leave your disk.
03
Apr

Linux Snippets #1: Auditing Network Visibility with ss
Your Linux system is constantly initiating connections in the background. Learn how to use the modern ss command to instantly audit active network sockets, expose chatty processes, and take back control of your data sovereignty.

