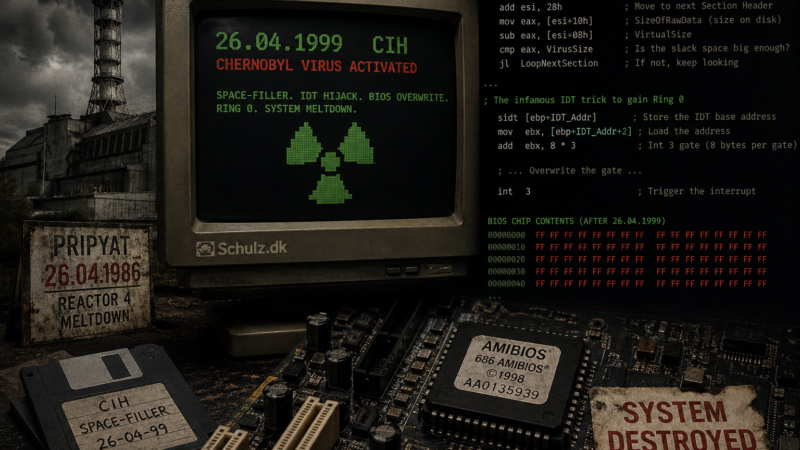
April 26 marks the 40th anniversary of the Pripyat disaster. It also marks the detonation date of the most destructive virus of the 90s: the CIH space-filler
2026
24
Apr
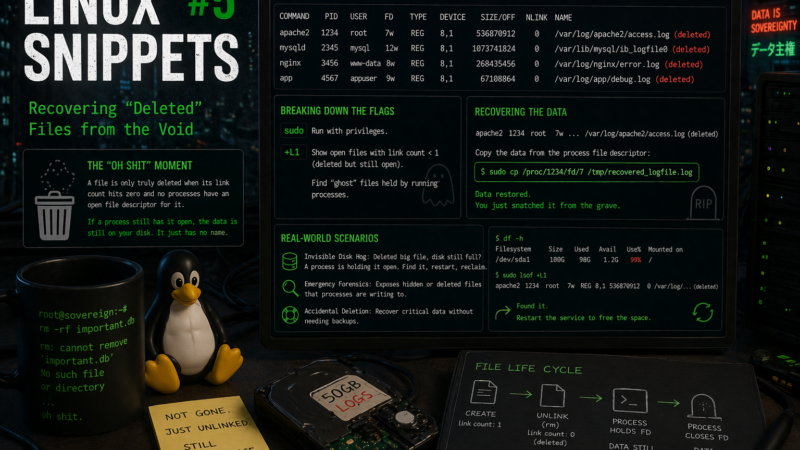
Linux Snippets #5: Recovering “Deleted” Files from the Void
Accidentally ran rm on a massive log file or a database while a process was still writing to it? Before you panic, learn how to use lsof to find the ‘ghost’ file in the /proc filesystem and snatch your data back.
21
Apr
Break through the wall
Discover a nerdy AI-generated song (sorry) about breaking firewalls and setting data free, transformed from quirky Danish lyrics into surprisingly catchy music.
20
Apr
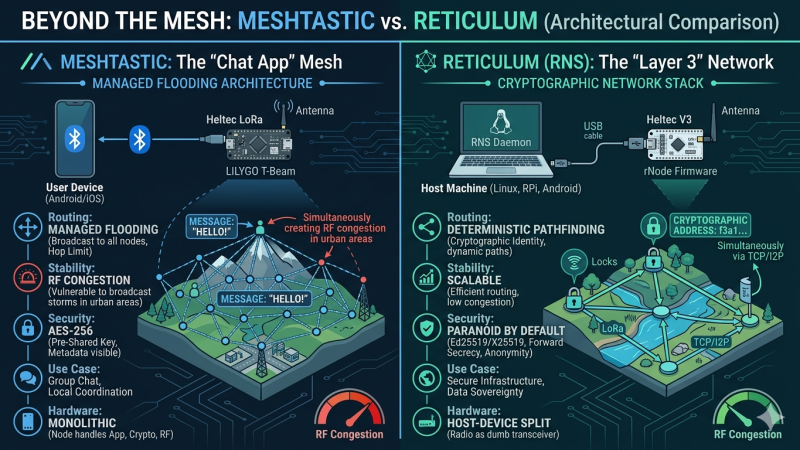
Meshtastic vs Reticulum: Why Reticulum Wins for Scalable Sovereign LoRa Networks
Meshtastic is currently dominating the off-grid communication hype cycle. But when we look under the hood at its managed flooding architecture and symmetric cryptography, does it actually hold up as a foundation for sovereign infrastructure? Here is a deep dive into why I am shifting my focus to the Reticulum Network Stack.
06
Apr

The Cryptographic Zombie: How Keybase Went from Privacy Darling to Zoom’s Cleanup Crew
Once the ultimate geek flex for cypherpunks, Keybase promised to make PGP cryptography accessible to mere mortals. Today, it hovers in the digital ether as a “zombie” app. Here is the story of how a revolutionary open-source identity platform was cannibalized to become Zoom’s corporate cleanup crew.
01
Mar
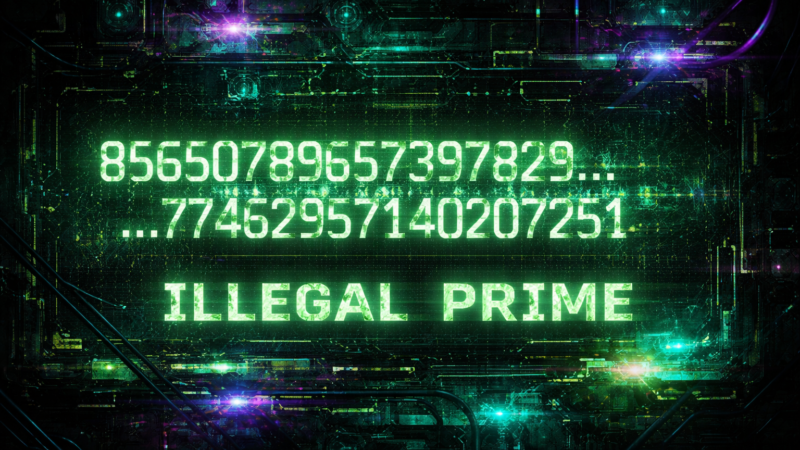
The Illegal Prime: When Math Became Contraband
March 2026 marks the 25years anniversary for something beautiful – A number….illigal number!
15
Jan
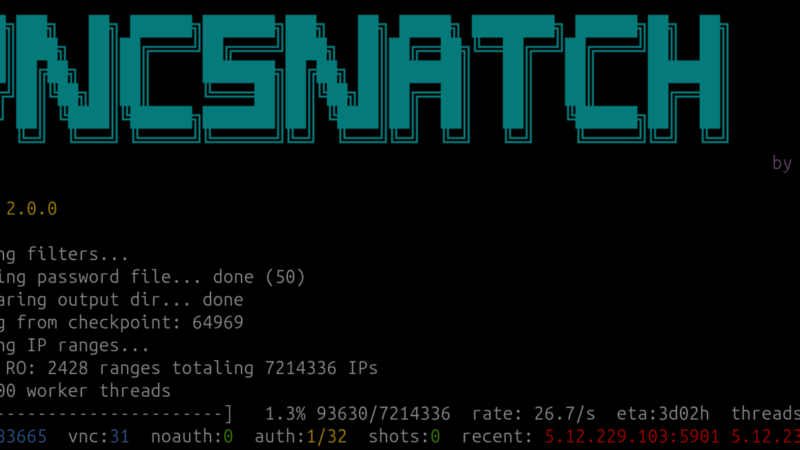
When Critical Infrastructure meets VNC on the open Internet
Did you know that a lot of critical infrastructure, factories, and much much more is easily accessible (and controllable) via VNC? One of my pet projects made me realize just how bad it is.
2025
24
Sep

Malware with a Mind of Its Own – a case study in 4 acts
A new armsrace has begun and in many ways it seems like we have started something we cannot stop again – like Skynet, but real!
So I set out to explore this a bit and write about it.
27
Apr

“What Has the EU Ever Done for Us?”
“What has EU ever done for us? – something I hear quite often. This time I actually think they did something that could potentially be good for mobile/tablet owners (me included)
23
Apr

Making Citrix Workspace Work on Ubuntu 24.04
had to access citrix for work the other day. It usually works acceptable but not this time…nothing! after some debugging I finally found a fix.