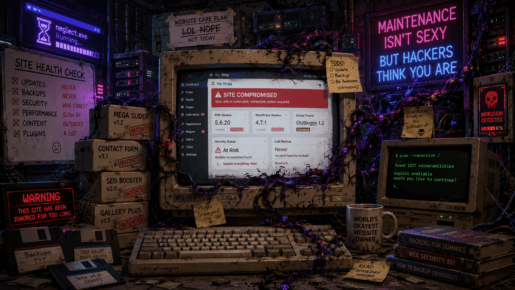
A WordPress backdoor hidden in functions.php is bad enough. One pasted after the closing ?> tag is almost poetic: malware that forgot to become PHP and instead printed its own confession. Here is a technical walk-through of a hidden admin account, query tampering, fake user counts, and the grim beauty of neglected WordPress hygiene.
2026
07
May
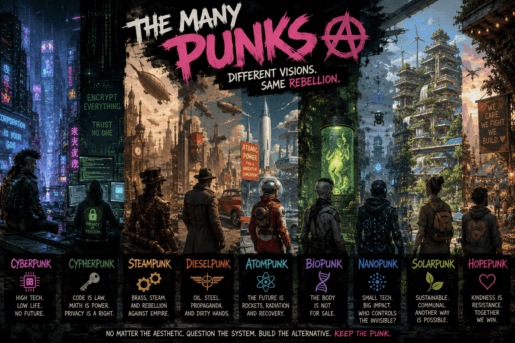
The Many Punks: A Field Guide to Futures That Refuse to Behave
The future is never just gadgets and skylines. Cyberpunk, solarpunk, cypherpunk, steampunk, and their unruly cousins are not merely aesthetics with goggles, neon, brass, or solar panels glued on top. They are arguments about power: who owns the machines, who gets watched by them, who repairs them, and who dares to build something better.
04
May

Rclone: Zero-Trust Cloud Storage Without the Friction
Stop trusting cloud providers with your personal data. Here is how to use rclone to build a transparent, client-side encryption layer over Dropbox or pCloud
29
Apr
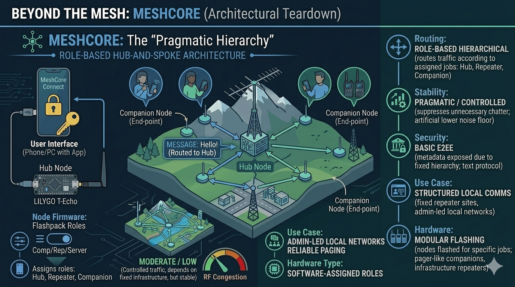
Beyond the Mesh: The MeshCore Paradime
Readers demanded to know where MeshCore fits into the off-grid landscape. It fixes RF congestion by forcing your radios into strict hierarchies. Here is why role-based routing is a brilliant band-aid but a severe regression for peer-to-peer sovereignty
26
Apr
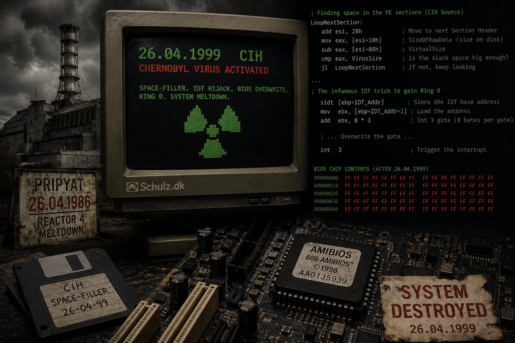
April 26: A 40-Year Anniversary of Meltdowns
April 26 marks the 40th anniversary of the Pripyat disaster. It also marks the detonation date of the most destructive virus of the 90s: the CIH space-filler
24
Apr
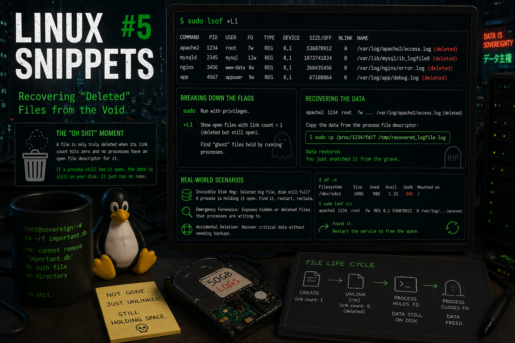
Linux Snippets #5: Recovering “Deleted” Files from the Void
Accidentally ran rm on a massive log file or a database while a process was still writing to it? Before you panic, learn how to use lsof to find the ‘ghost’ file in the /proc filesystem and snatch your data back.
23
Apr
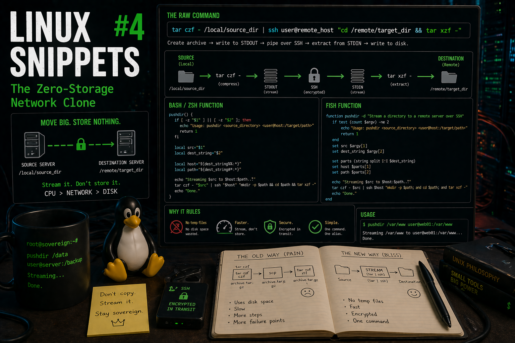
Linux Snippets #4: The Zero-Storage Network Clone
Stop filling up your disk with temporary zip files. Here is how to stream a directory directly from one server to another using tar and SSH in a single pipeline.
22
Apr

Github is watching you
github has a nice and easy cli tool to use, but if you thought that it would let you keep your privacy – think again!
21
Apr
Break through the wall
Discover a nerdy AI-generated song (sorry) about breaking firewalls and setting data free, transformed from quirky Danish lyrics into surprisingly catchy music.
20
Apr
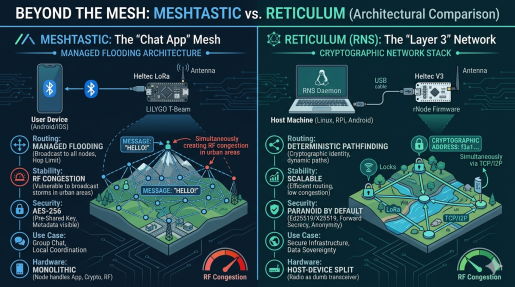
Meshtastic vs Reticulum: Why Reticulum Wins for Scalable Sovereign LoRa Networks
Meshtastic is currently dominating the off-grid communication hype cycle. But when we look under the hood at its managed flooding architecture and symmetric cryptography, does it actually hold up as a foundation for sovereign infrastructure? Here is a deep dive into why I am shifting my focus to the Reticulum Network Stack.