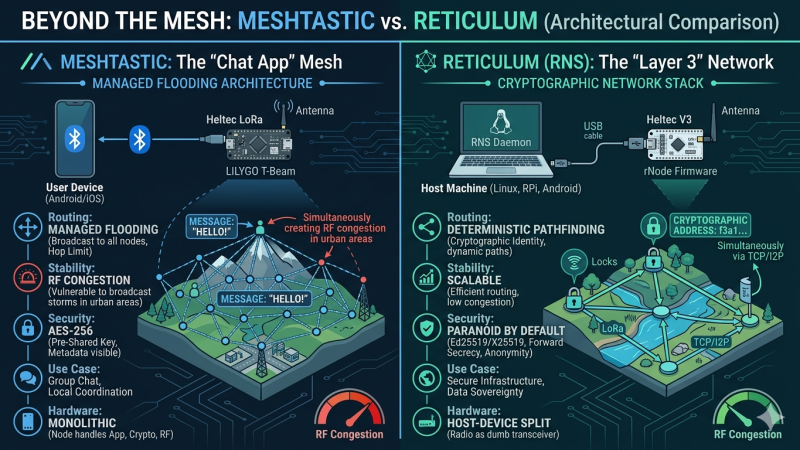
Meshtastic is currently dominating the off-grid communication hype cycle. But when we look under the hood at its managed flooding architecture and symmetric cryptography, does it actually hold up as a foundation for sovereign infrastructure? Here is a deep dive into why I am shifting my focus to the Reticulum Network Stack.
2026
10
Apr

Linux Snippets #3: The Instant SSH SOCKS Proxy
Skip the heavy VPN clients. Here is how to turn any remote Linux server into an encrypted SOCKS5 proxy with a single SSH command to bypass hostile local networks
06
Apr

The Cryptographic Zombie: How Keybase Went from Privacy Darling to Zoom’s Cleanup Crew
Once the ultimate geek flex for cypherpunks, Keybase promised to make PGP cryptography accessible to mere mortals. Today, it hovers in the digital ether as a “zombie” app. Here is the story of how a revolutionary open-source identity platform was cannibalized to become Zoom’s corporate cleanup crew.
2025
24
Sep

Malware with a Mind of Its Own – a case study in 4 acts
A new armsrace has begun and in many ways it seems like we have started something we cannot stop again – like Skynet, but real!
So I set out to explore this a bit and write about it.
2024
25
Oct

The Paradox of Privacy in the Digital Age
Having a philosophical moment thinking about my own privacy, I took a trip back through the history of the concept “privacy” by following the simple question: “Do you have privacy?”
03
Sep

Chat in the Shadows: Dark IRC on Linux for Maximum Privacy
So, you’ve heard about the Telegram fiasco, right? The big guy in charge got thrown in the slammer in France, and everyone started panicking about who’s really in control of our messages. If that doesn’t scream, “Hey, maybe don’t trust centralized platforms,” then I don’t know what will. But don’t worry! This guide is here […]
01
Feb
Unveiling the Evolution: A Historical Journey through Computer Viruses
Exploring the evolution of computer viruses from the 1970s to present times, where I discuss the continuous battle between ever-evolving cyber threats and advancing cybersecurity. From pioneering malware like Creeper and Brain to the widespread destruction caused by I Love You and SQL Slammer, each era demonstrates escalating sophistication and societal impact, emphasizing the need for proactive security measures, education, and global collaboration to combat and adapt to these persistent cyber threats.
2023
23
May

Python virus for fun and profit
Can you write a self-replicating virus in python? I gave it a try.
2022
26
Jan

CVE-2021-4034 – my PoC for PwnKit
I made a Proof of Concept exploit (two actually) for the new Polkit CVE posted yesterday. Find a description and code here.
2021
04
Jun

Who shares private social security number online?!?!
Have you ever shared a picture of your Danish social security card (in Danish: sundhedskortet) online? Maybe with a finger across to cover the secret number?
Think you’re safe from identify theft? probably not!