github has a nice and easy cli tool to use, but if you thought that it would let you keep your privacy – think again!
2026
22
Apr
20
Apr
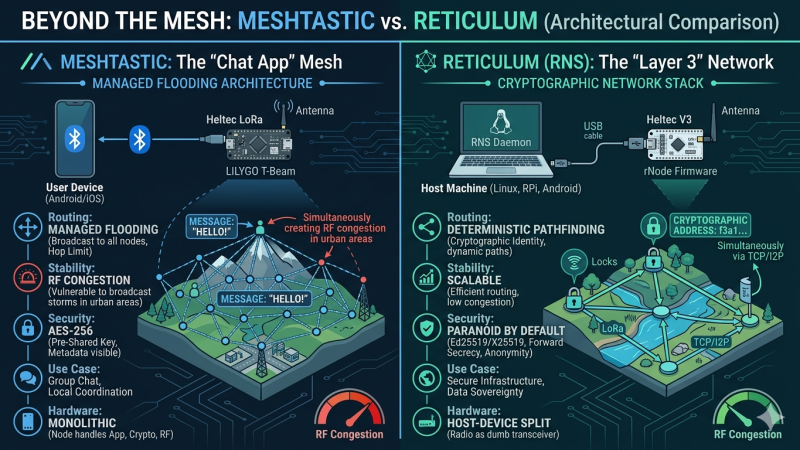
Meshtastic vs Reticulum: Why Reticulum Wins for Scalable Sovereign LoRa Networks
Meshtastic is currently dominating the off-grid communication hype cycle. But when we look under the hood at its managed flooding architecture and symmetric cryptography, does it actually hold up as a foundation for sovereign infrastructure? Here is a deep dive into why I am shifting my focus to the Reticulum Network Stack.
10
Apr

Linux Snippets #3: The Instant SSH SOCKS Proxy
Skip the heavy VPN clients. Here is how to turn any remote Linux server into an encrypted SOCKS5 proxy with a single SSH command to bypass hostile local networks
05
Apr
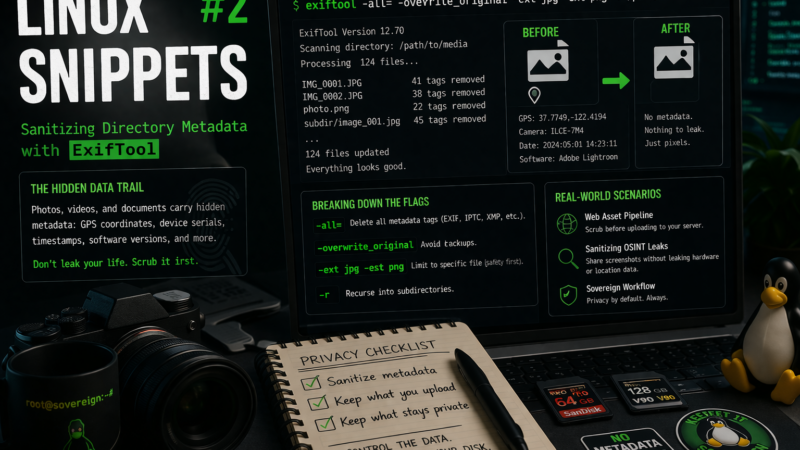
Linux Snippets #2: Sanitizing Directory Metadata with ExifTool
Blindly uploading images to the web is a massive privacy leak. Here is how to use exiftool to recursively strip hidden GPS and hardware metadata from your staging directories before they ever leave your disk.
2025
14
May

The Political Climate Is a Cybersecurity Problem – And It’s Time to Move Your Data
In a world where cloud giants are entangled with global surveillance and legal overreach, trusting your data to ‘neutral’ infrastructure is a risky illusion. This post dives into why geopolitical tension is now a cybersecurity issue – and why it’s smarter than ever to store your data locally, or at least within the EU
2024
25
Oct

The Paradox of Privacy in the Digital Age
Having a philosophical moment thinking about my own privacy, I took a trip back through the history of the concept “privacy” by following the simple question: “Do you have privacy?”
03
Sep

Chat in the Shadows: Dark IRC on Linux for Maximum Privacy
So, you’ve heard about the Telegram fiasco, right? The big guy in charge got thrown in the slammer in France, and everyone started panicking about who’s really in control of our messages. If that doesn’t scream, “Hey, maybe don’t trust centralized platforms,” then I don’t know what will. But don’t worry! This guide is here […]
2022
24
Nov

Better mobile privacy via FOSS
Android is great but from a privacy perspective there is a lot to be desired.
At least some of it can be fixed by installing FOSS (Free & Open Source Software) alternatives to common apps. Here I have assembled some of my favorites – Enjoy!

