If you follow the decentralized hardware space, it is hard to miss the rapid rise of Meshtastic. It has achieved exactly what it set out to do: reduce the barrier to entry for LoRa-based communication to nearly zero. You can buy an inexpensive $30 development board—sometimes for as little as $5 from China—flash it directly from a Chrome browser, pair it with your phone over Bluetooth, and almost instantly start chatting with strangers on the default LongFast channel. It feels almost magical.
But as any seasoned sysadmin knows, “magic” in computer science usually just means someone else is hiding a massive pile of complexity – and structural compromises – from you.
As I began looking at building permanent, sovereign infrastructure – networks designed to survive internet outages, deliberate censorship, and the general enshittification of the modern web – the cracks in the Meshtastic architecture became glaringly obvious. It works beautifully until you want to scale it beyond its rigid, chat-oriented parameters. This realization led me to test an entirely different, and frankly much less forgiving, paradigm: the Reticulum Network Stack (RNS) running over the rNode firmware.
To understand why Reticulum is a structurally superior foundation for serious networks, we have to stop looking at the shiny mobile apps and start looking at how these systems handle routing, stability, and cryptography at the protocol level.
The Meshtastic Illusion: Managed Shouting
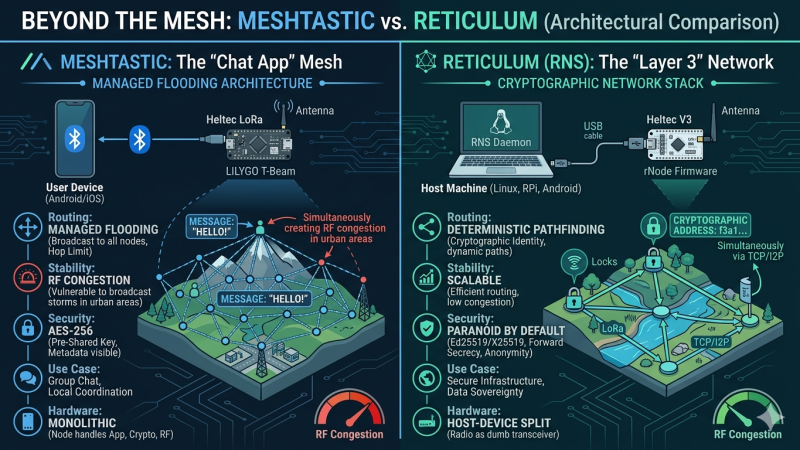
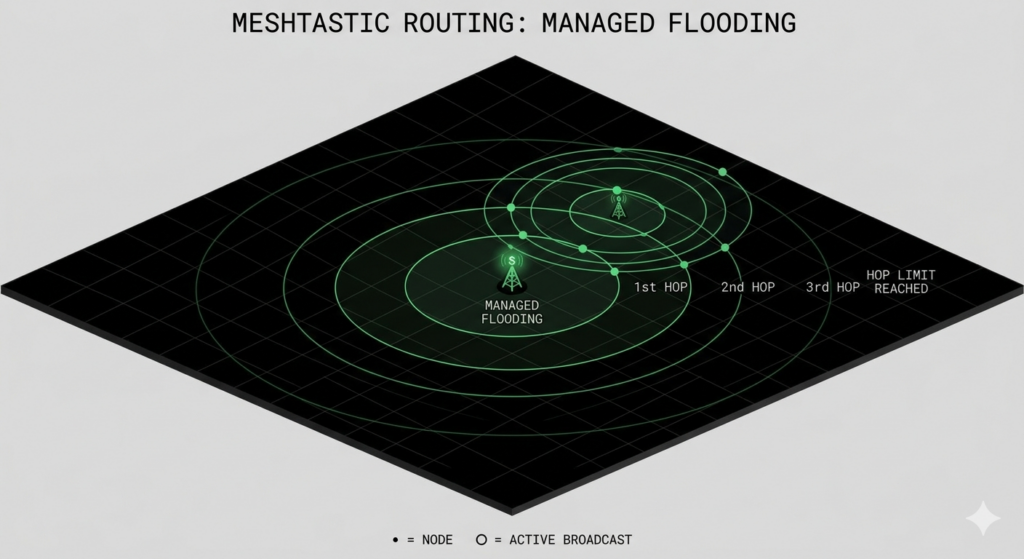
The core limitation of Meshtastic lies in its routing algorithm. Let’s be clear: Meshtastic is not a true network protocol in the traditional sense. It is a broadcast chat application built on a concept called “managed flooding.”
When you send a message to a group channel on Meshtastic, you are essentially relying on blind replication. Your node broadcasts the encrypted packet, and any receiving node within range repeats that packet until the message hits its destination or its “Hop Limit” (Time To Live) expires.
While the developers have implemented clever band-aids – like preferring nodes with better signal margins to act as repeaters – it is still, fundamentally, a system of managed shouting.
In a network with twenty nodes spread out over a rural forest, flooding is incredibly resilient. In a dense urban environment with hundreds of nodes, it creates broadcast storms. The airwaves become so congested with nodes talking over each other and re-transmitting the exact same packets that the noise floor rises, packet collisions skyrocket, and the entire mesh suffers from the hidden terminal problem. You are forced into micro-managing transmission delays, duty cycles, and airtime limits just to keep the network from choking itself to death on its own echo.
Enter Reticulum: Layer 3 Sanity
Reticulum operates on a fundamentally different level of the OSI model. It is a true cryptography-based networking layer – a Layer 3 stack. It does not care if your physical medium is a LoRa radio, a dedicated fiber line, an I2P tunnel over the open internet, or an acoustic modem bolted to a submarine.
When you flash a LoRa board like a Heltec V3 with the rNode firmware(the LoRa firmware for reticulum), you are stripping away all application logic. You turn that piece of hardware into a dumb RF transceiver.
All the intelligence, routing, and cryptography is moved off the tiny, underpowered ESP32 microcontroller and onto a host machine. That host could be a Linux laptop running the rnsd daemon, a Raspberry Pi strapped to a solar panel, or an Android phone running an app like Sideband.
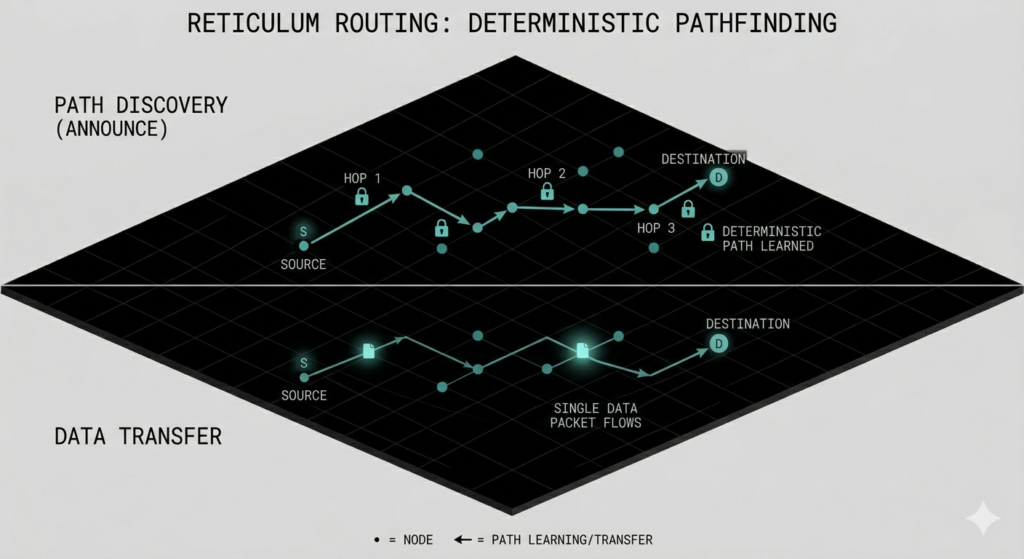
This “host-device split” allows Reticulum to abandon blind flooding entirely in favour of deterministic, cryptographic addressing.
No IP Addresses: Cryptography as Destination
In Reticulum, there are no IP addresses or MAC addresses to spoof or track. A destination is simply a 16-byte hash derived from an Ed25519 public key.
You do not ask the network to broadcast a message to everyone and hope it gets there. Instead, the network builds dynamic paths based on path discovery announcements. If your Linux laptop is connected to an Ethernet LAN, an I2P tunnel, and an rNode radio simultaneously, Reticulum will automatically calculate the most efficient path. It will route the encrypted data across all these disparate physical layers seamlessly to reach its cryptographic destination. It is true heterogeneous routing.
This architectural difference directly impacts the security and privacy of the network in profound ways:
Meshtastic uses a Pre-Shared Key (PSK) model utilizing AES256. If you have the channel key, you can decrypt the traffic on that channel. Direct messages use a derivation of this, but much of the routing metadata remains visible. Anyone with a receiver can see who is talking, how often, and often infer their physical proximity based on signal-to-noise ratios and telemetry packets. If one node on your private channel is physically compromised, the security model of the entire channel shatters.
Reticulum, by contrast, is paranoid by default. It is built on absolute initiator anonymity and perfect forward secrecy. It uses Ed25519 for cryptographic signatures and X25519 for Elliptic-Curve Diffie-Hellman key exchanges. Every time you establish a link with another node, ephemeral keys are generated. Even if a hostile actor records months of your encrypted radio traffic and later physically compromises your device to extract your private keys, they *cannot* decrypt the past traffic. Furthermore, Reticulum packets do not contain source addresses. An eavesdropper cannot tell who generated a packet, only the cryptographic destination it is heading towards.
To summarize the operational realities of these two systems, we can look at them side by side:
| Feature / Architecture | Meshtastic | Reticulum Network Stack (with rNode) |
| Usability | Excellent. Plug-and-play with polished mobile apps | Brutal (for non-techies). Requires managing host environments, configs, and raw hardware |
| Network Stability | Vulnerable to broadcast storms and RF congestion at scale. | Highly scalable; eliminates redundant transmissions via smart routing. |
| Cryptography | AES256 with Pre-Shared Keys (PSK). Vulnerable to metadata analysis | d25519 / X25519. Perfect Forward Secrecy and Initiator Anonymity. |
| Hardware Architecture | Monolithic. The radio chip handles App, Crypto, and RF. | Host-Device split. Radio acts as a transceiver; PC/Phone handles logic. |
| Heterogeneous Routing | Limited to LoRa and specific IP gateway bridges. | Native. Seamlessly routes across LoRa, Packet Radio, Ethernet, and I2P. |
Which one should I choose?: Convenience vs. Control
The trade-off here is ultimately between user convenience and absolute architectural control.
If your goal is to coordinate who brought the IPAs on a weekend camping trip, or you just want to drop a few solar nodes around your neighborhood to chat with locals, Meshtastic is fantastic. It works right out of the box, and the UI is practically foolproof.
But if your goal is to build a sovereign communication infrastructure that you actually own – one that cannot be spoofed, cannot be tracked via metadata, and isn’t dependent on a specific hardware vendor or a fragile flooding algorithm – Meshtastic is essentially a gateway drug. Reticulum is the actual foundation.
You will likely question your life choices while configuring Python virtual environments and trying to cleanly mount a Heltec board to the back of your phone with a right-angle USB-C cable (I will see if I can share my 3d prints for that soon). But once the link is established, you are running a piece of the internet that belongs entirely to you.
Over to you: Have you hit the scalability wall with Meshtastic in your local urban mesh yet? Or are you currently tumbling down the Reticulum rabbit hole like I am? Drop a comment below or find me on the fediverse – I’d love to hear what hardware you are trusting for your off-grid builds