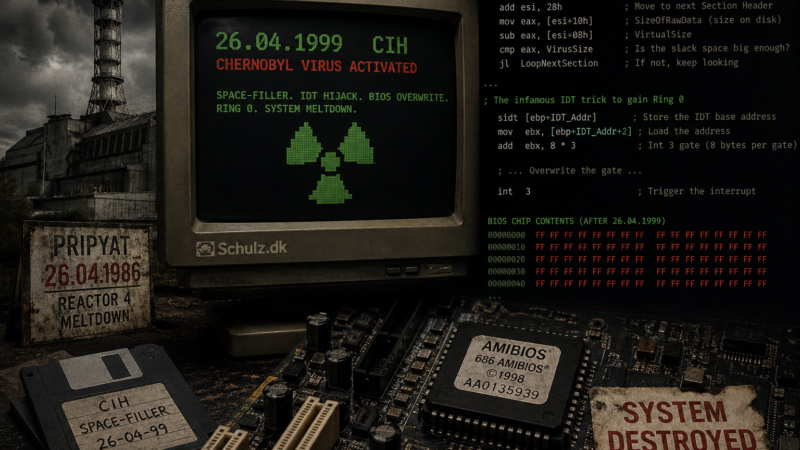
April 26 marks the 40th anniversary of the Pripyat disaster. It also marks the detonation date of the most destructive virus of the 90s: the CIH space-filler
2026
22
Apr

Github is watching you
github has a nice and easy cli tool to use, but if you thought that it would let you keep your privacy – think again!
20
Apr
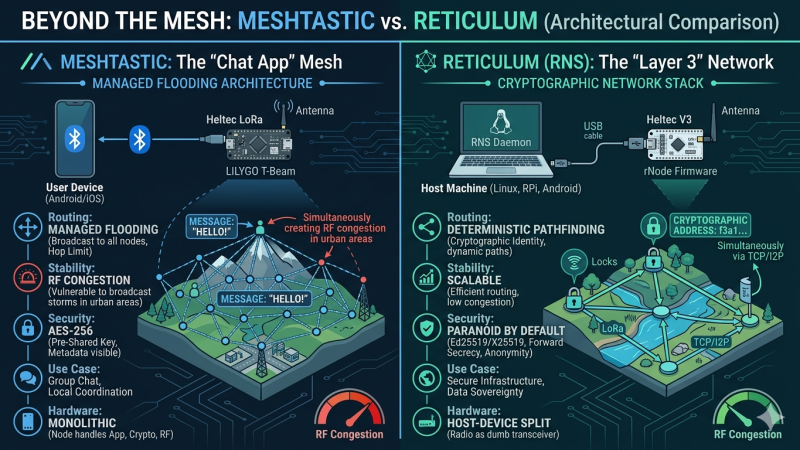
Meshtastic vs Reticulum: Why Reticulum Wins for Scalable Sovereign LoRa Networks
Meshtastic is currently dominating the off-grid communication hype cycle. But when we look under the hood at its managed flooding architecture and symmetric cryptography, does it actually hold up as a foundation for sovereign infrastructure? Here is a deep dive into why I am shifting my focus to the Reticulum Network Stack.
06
Apr

The Cryptographic Zombie: How Keybase Went from Privacy Darling to Zoom’s Cleanup Crew
Once the ultimate geek flex for cypherpunks, Keybase promised to make PGP cryptography accessible to mere mortals. Today, it hovers in the digital ether as a “zombie” app. Here is the story of how a revolutionary open-source identity platform was cannibalized to become Zoom’s corporate cleanup crew.
2025
24
Sep

Malware with a Mind of Its Own – a case study in 4 acts
A new armsrace has begun and in many ways it seems like we have started something we cannot stop again – like Skynet, but real!
So I set out to explore this a bit and write about it.
27
Feb

Random MAC address for anonymity
Ever feel like your phone is snitching on you? That’s because it probably is — at least, its MAC address is. In this deep-dive post, we explore how your devices quietly broadcast your identity through Wi-Fi and Bluetooth, and how you can fight back by randomizing your MAC address. From Linux laptops to iPhones and Androids, we break down how to go full digital chameleon, one spoofed packet at a time. Bonus points for keeping your sneakers-buying habits off the grid.
2024
09
Oct

How to crash macOS Sequoia in 10 lines of code
Apple always brag about the stability of their products, and this is a claim that their users tend to echo. Having had a debugger connected to macOS and IOS more than a few times, I know that it is more about hiding the crashes than actually preventing them (it is amazing how often the IOS […]
03
Sep

Chat in the Shadows: Dark IRC on Linux for Maximum Privacy
So, you’ve heard about the Telegram fiasco, right? The big guy in charge got thrown in the slammer in France, and everyone started panicking about who’s really in control of our messages. If that doesn’t scream, “Hey, maybe don’t trust centralized platforms,” then I don’t know what will. But don’t worry! This guide is here […]
01
Feb
Unveiling the Evolution: A Historical Journey through Computer Viruses
Exploring the evolution of computer viruses from the 1970s to present times, where I discuss the continuous battle between ever-evolving cyber threats and advancing cybersecurity. From pioneering malware like Creeper and Brain to the widespread destruction caused by I Love You and SQL Slammer, each era demonstrates escalating sophistication and societal impact, emphasizing the need for proactive security measures, education, and global collaboration to combat and adapt to these persistent cyber threats.
2023
23
May

Python virus for fun and profit
Can you write a self-replicating virus in python? I gave it a try.